More Salesloft Drift Compromise: Expanding to more apps than Salesforce
Attackers stole OAuth tokens from Salesloft Drift, hitting Salesforce & Gmail. WideField recommends revoking all Drift app connections & tightening 3rd-party integration controls.
Background
Salesloft acquired Drift in February 2024. Salesloft provides many products, some branded under Salesloft, others still under the Drift brand.
The Drift product line provides a chatbot interface into a variety of sales and marketing platforms like CRM systems for customer records, marketing automation tools for nurturing, calendars for scheduling, and sales platforms for follow-up. Some products were acquired such as Siftrock in September 2018 which became Drift Email, referenced later in this blog.
The Salesloft-branded product line helps sales teams keep track of their deals, follow up with customers, and know what to do next to close more sales.
Clari announced acquisition plans for Salesloft in August 2025.
This background is provided for context for the different products involved in the security incident in this blog. Salesloft will primarily be used to refer to the company and Salesloft Drift or Drift will be used to refer to the Drift product line.
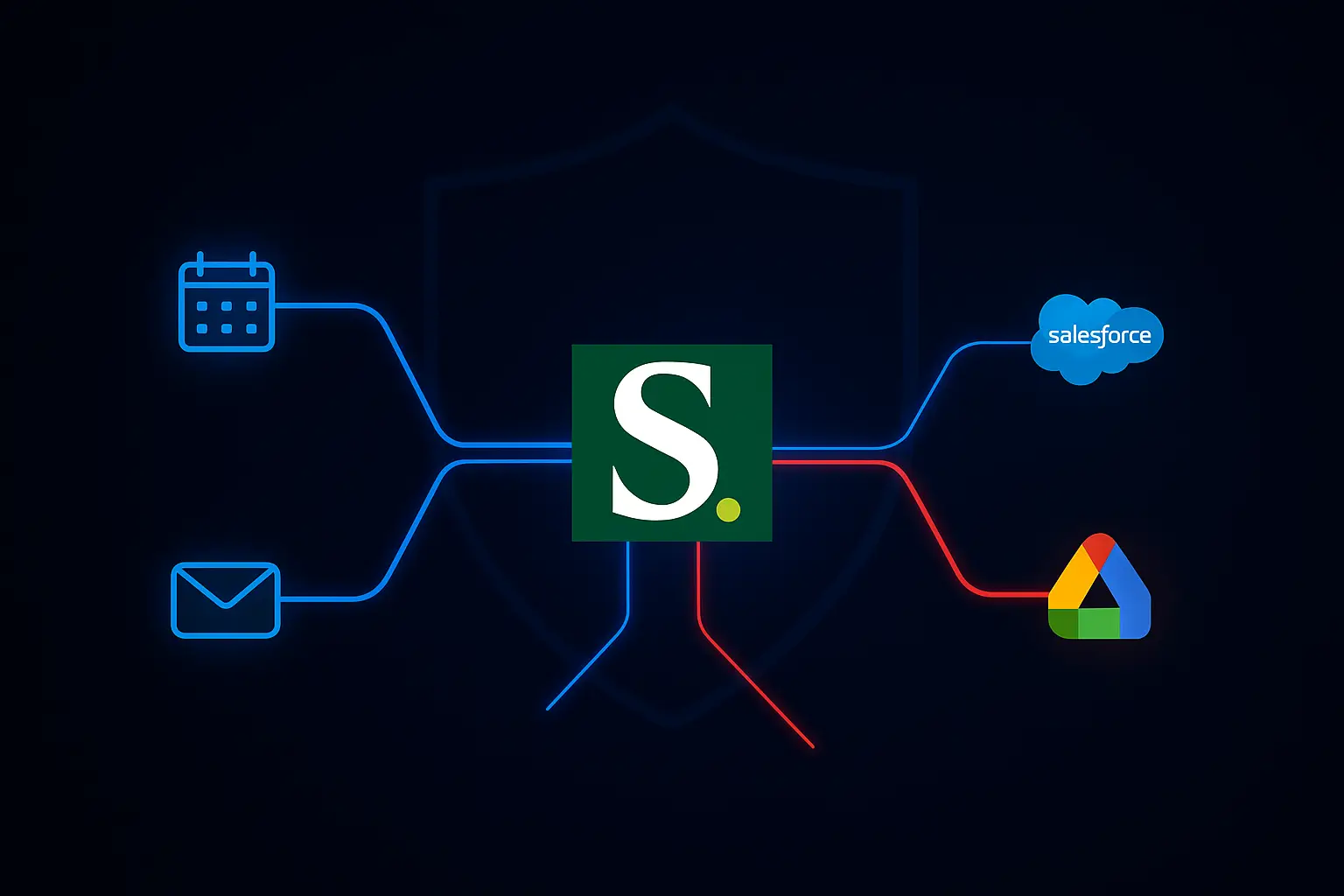
Salesloft Drift Connected App Model (OAuth)
On a technical level, the Drift products connect as OAuth applications to target resource environments such as Salesforce, Gmail, Microsoft. Drift products would normally be referred to as connected apps or 3rd-party apps, and often be implemented as OAuth client apps using OAuth 2.0 for authorization and connectivity.
Salesloft Drift Access Flow Diagram (normal)
Normally, Drift and 3rd-party applications have a run-time access architecture like this:

The access paths are granted by users or possibly by administrators (for the whole organization/tenant) via OAuth flows and granting user permissions to the Drift product(s) to access user data in the target app environment.
The granting process involves standard OAuth flows, with the user directed to the trusted resource provider for authentication including MFA e.g. Salesforce. After user authentication/authorization, the Drift application will receive OAuth refresh and access tokens from Salesforce that can be used for API access to user data and resources in Salesforce. The permissions of the OAuth tokens are specified as part of the authorization request by the Drift application and presented to the user during their authorization step.
Salesloft Drift-Salesforce Compromise reported by Salesloft/GTIG
The Drift application integration with Salesforce had a security incident in August 2025. Here is the relevant information and timelines.
August 19-25: Salesloft Security Notifications
- Reference: https://trust.salesloft.com/?uid=Drift%2FSalesforce+Security+Notification
- Time period of incident: Aug 8-18, 2025
- Incident: Salesloft reported a security incident (breach) of their Drift platform, with threat actors obtaining active Drift-Salesforce OAuth access tokens (stored by the Drift application). Initial compromise vector of how OAuth access tokens were obtained is not known or disclosed.
- Impact: The OAuth tokens were valid and provided API access to customer Salesforce instances. Salesforce customers using Drift are affected. More than 700 Salesforce customers potentially impacted, according to a Google Threat Intelligence Group analyst.
- Updates (Salesloft security update August 25, 2025)
- The incident did not impact customers who did not use the Drift-Salesforce integration.
- A third party digital forensics and incident response (DFIR) firm hired
- Follow-on threat actor activity: The threat actor downloaded content from Salesforce, discovering in some cases insecurely stored secrets such as AWS access keys, VPN credentials, Snowflake credentials as seen by Salesforce activity with the compromised OAuth tokens. Storage of secrets in Salesforce is an insecure practice unrelated to the Drift incident, but was apparently discovered in targeted environments, so certain related TTP were observed.
- Recommendations from Salesloft: revoke then reauthorize Drift connected app connections within Salesforce.
August 26: Mandiant/Google Threat Intelligence Group (GTIG) Blog
- https://cloud.google.com/blog/topics/threat-intelligence/data-theft-salesforce-instances-via-salesloft-drift
- Mandiant/GTIG confirms details including IOCs such as IPs used by threat actors when using the compromised OAuth tokens.
Salesloft Drift → Salesforce Attack Diagram (compromise)
The prior Salesloft Drift security notices imply the following occurred:

- Salesloft Drift datacenters were breached by UNC6395. Access vector unknown or undisclosed.
- OAuth tokens were compromised and exfiltrated
- Threat actor used OAuth tokens over proxy IPs to gain access to Salesforce instances of various organizations (Customer A). The threat actor performed discovery of Salesforce data, found in some cases various secrets used for other environments and continued the attack.
The threat actor used various proxy IPs (many Tor, some not). The IP list is the part of the IOCs included in the security notices published by Salesloft/GTIG. Any traffic from Tor exit node IPs have clear high risk; they are also shared among the Tor network and can include activity from multiple threat actors over the same time period resulting in possible misattribution.
Once access to Salesforce was gained, discovery was done on Salesforce objects. Based on subsequent activity analyzed by GTIG, it appears the threat actor found additional secrets stored insecurely by some of the organizations within their Salesforce instance. This resulted in further access to other environments in those organizations like AWS, Snowflake and VPN/SSO. The TTP in terms of Salesforce queries used to count objects, retrieve user data, and case data can be searched for when investigating incidents or threat hunting. These queries are described in the GTIG blog.
Salesloft Drift Email-Google Potential Compromise detected by WideField
Summary
WideField observed suspicious log event activity across multiple WideField customers being monitored by the WideField Security Platform. All of the source IPs found in customer logs were on the malicious IP list identified by GTIG.
- Time period: Aug 9-19 (same time period as reported in Salesloft Drift-Salesforce compromise)
- Total log events: 191
- Applications: Gmail, Salesforce
- Source IP addresses: all matching the GTIG reported IOCs
Details
- Gmail accessed (additional compromise)
- Timeframe: August 9, 2025
- Activity: successful use of OAuth tokens for gmail access
- Events: 183 events
- Users: 3 accounts in 1 organization
- IP addresses: 44.215.108.109
- Client app: Salesloft Drift Email
- Client app id: 1084253493764-ipb2ntp4jb4rmqc76jp7habdrhfdus3q.apps.googleusercontent.com
- Operation: gmail.users.messages.get
- Salesforce accessed (original compromise)
- Timeframe: August 12 - 18, 2025
- Activity: OAuth refresh token activity (confirming original compromise)
- Events: 8 events
- Users: 1 account in 1 organization
- IP addresses: 44.215.108.109, 208.68.36.90
- Client app: Salesloft Drift
The Gmail related log activity strongly indicates that there was broader compromise by the threat actor due to these indicators:
- The 183 events were from 1 IP address, which was on the GTIG IOC list
- The IP address is a non-Tor exit node IP address. Tor exit nodes, while highly suspicious are also shared and can be from other threat actor activity.
- The IP address is not on the Drift Whiltelist Domains and Public IP Address KB article updated August 24, 2025.
- The OAuth tokens were created from a grant to Drift Email based on the client id
- The OAuth tokens were valid and the activity successfully retrieved email data
- The timeframe is within the original incident timeframe
Salesloft Drift Email → Gmail Attack Diagram (compromise)

- The threat actor breached Salesloft Drift data centers
- They were able to obtain additional OAuth tokens, including Salesloft Drift-Email and exfiltrate them.
- The OAuth tokens were valid and used against different organizations (Customer B) that included a WideField customer.
Analysis
WideField SIRT has concluded that there is strong evidence of additional threat actor activity related to the Salesloft Drift compromise but beyond Drift-Salesforce customers. Salesloft Drift Email-Google customers have also had OAuth session tokens compromised.
WideField recommends immediate and broader remediation efforts as described below.
Recommended Guidance
WideField recommends that every customer using any Salesloft Drift products more broadly revoke access and investigate fully potential compromised identities and sessions.
Broad access revocation
Immediately revoke all connected app connections for all users related to any Salesloft Drift products in use, not just Drift-Salesforce.
Here is a summary of Drift Products and example target applications that are integrated:
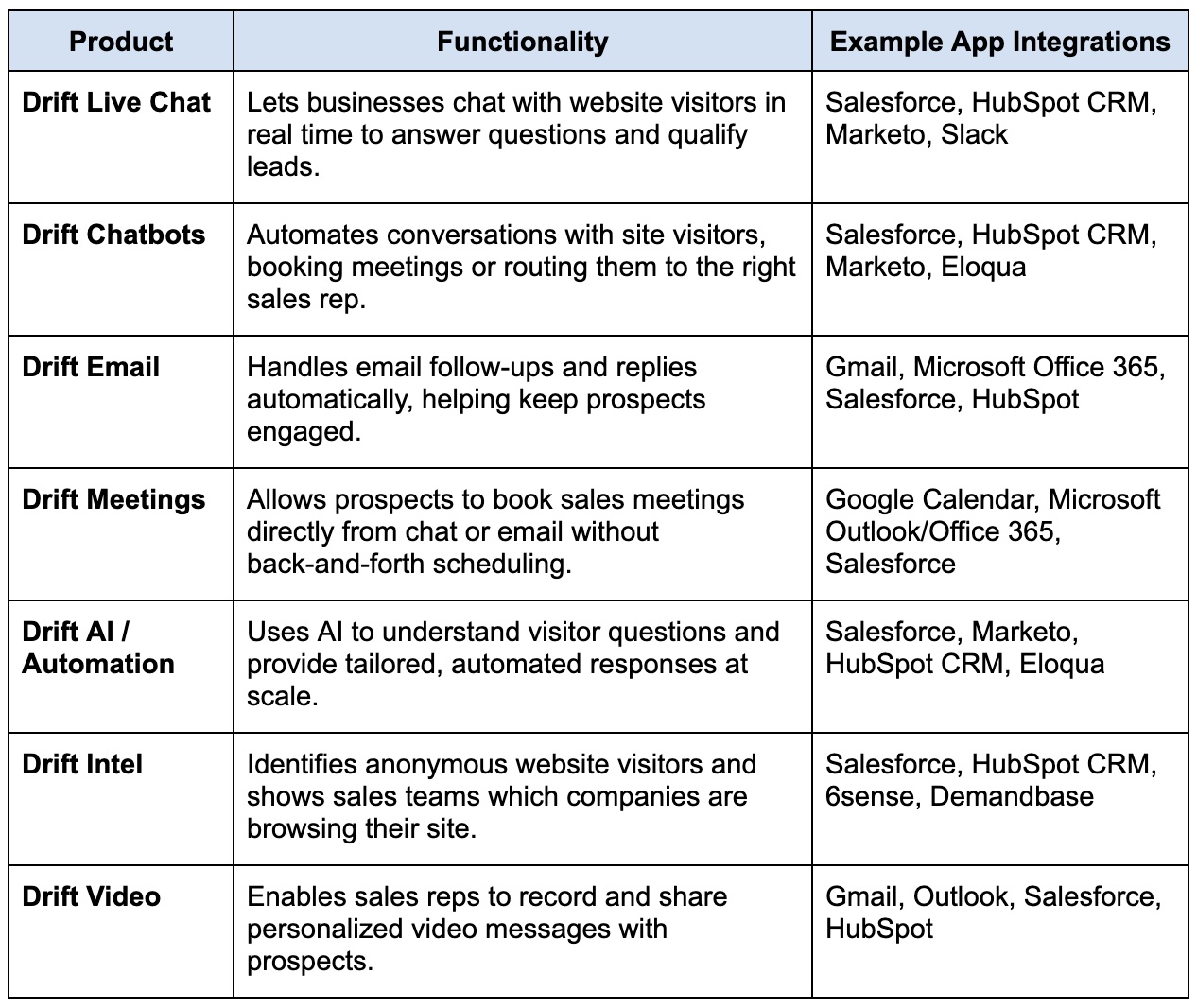
* Note: each integration’s documentation should be read to provide visibility into the permissions requested in order to assess full impact if compromised. For example, the Salesloft Drift integration with Microsoft allows admin level grants to connect all user’s calendars, which impacts incident investigation and remediation efforts.
Reauthorizing of the app connections (e.g. Drift access) typically will revoke existing connections (and tokens) but this must be verified through vendor documentation and testing.
Full compromise assessment
Any accounts associated with Salesloft Drift OAuth application access in the timeframes of the incident should be assumed to be compromised and IR procedures followed and credentials rotated at a minimum.
Additionally, any users who were active in Drift products in the time period of August 8-18 should have their activities reviewed for any suspicious or abnormal behavior. The GTIG report should be reviewed for the types of suspicious post-compromise activity observed in compromised customers and these should be guides for log queries.
Customers should review their Salesforce instances for accidental secrets storage. If found, move the secrets to a secure vault, delete them from Salesforce, and then perform an investigation specifically for suspicious activity in the applications and accounts related to those secrets.
Ongoing risk management
For risk management purposes, customers should start to:
- review external 3rd-party application integrations to reduce attack surface
- create an approved application list for 3rd-party connected apps with tight consent controls
- remove user consent for 3rd-party apps
- implement and tighten protection measures such as refresh token policies and token timeouts
- review detection login for post-access TTPs
- review, retest, and update access revocation procedures in SecOps runbooks, with a focus on token revocation
- create a repeatable and measurable process
If any compromise was detected, these risk management activities should be prioritized immediately, because they relate to reducing the identity attack surface of connected applications, which is at the very core of the Salesloft Drift security incidents.
WideField guidance for customers
The WideField Security Platform provides several features for detecting and responding to both the original Drift compromise and Drift Email compromise:
- Detections
- Existing OAuth token abuse findings will flag the use of compromised OAuth tokens as anomalous activity based on some of the malicious indicators associated with this incident or with behavioral analysis of post-breach activity.
- These are enabled out-of-the-box and do not require configuration.
- These findings are automatically sent to SIEM integrations if configured.
- Remediation
- Multiple actions including termination of all or specific sessions or revocation of access can be taken.
- Manual remediation can be performed within the WideField Console.
- Automatic remediation can be implemented within the Policy Engine.
- Analysis, Investigation, Threat-Hunting
- Connected application analytics (filter: connected app == Salesloft | Drift) can highlight external application access that has been granted and used
- Account analytics lists details about service accounts or service principals used for access, verifies roles and permissions, provides broader activity timelines on the accounts, and can list active sessions.
Assessment
Broad compromise
- Strong evidence of additional Drift Email OAuth token compromise was found.
- Customers should assume connections to all Drift products are compromised and revoke/review/reauthorize these connections.
- Customers should review and investigate all accounts that had activity related to Drift products during the time period of the incident.
Disclosure and ongoing analysis
- Complete log information is being shared immediately with WideField customers for remediation purposes.
- Communication has been initiated with GTIG in order to assist in more comprehensive analysis and understanding of the incident.
Updates
- WideField will assess any updates from Salesloft or GTIG concerning the initial access vectors of the original breach or downstream compromise.
- WideField SIRT will then reevaluate the incident, and push updated analysis/guidance to WideField customer SIRT contacts.
- Analysis that is useful to the broader community will be published as a WideField blog.
Better Security Practices
Secrets management
The storage of secrets (presumably unencrypted) in Salesforce by some of the compromised organizations was unrelated to the incident but shows that other insecure practices can magnify the impact of breaches. Secrets storage best practices are well-known
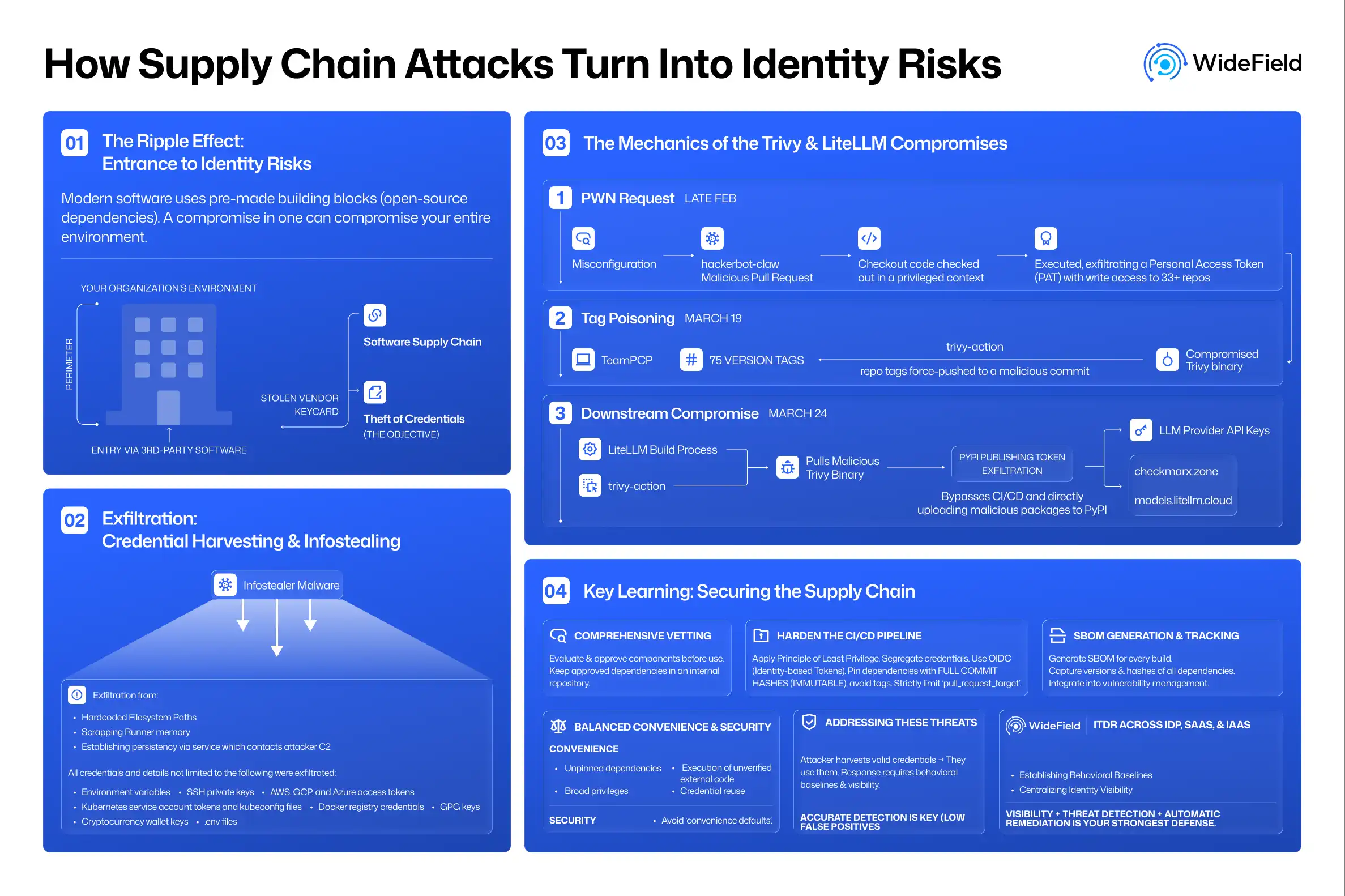
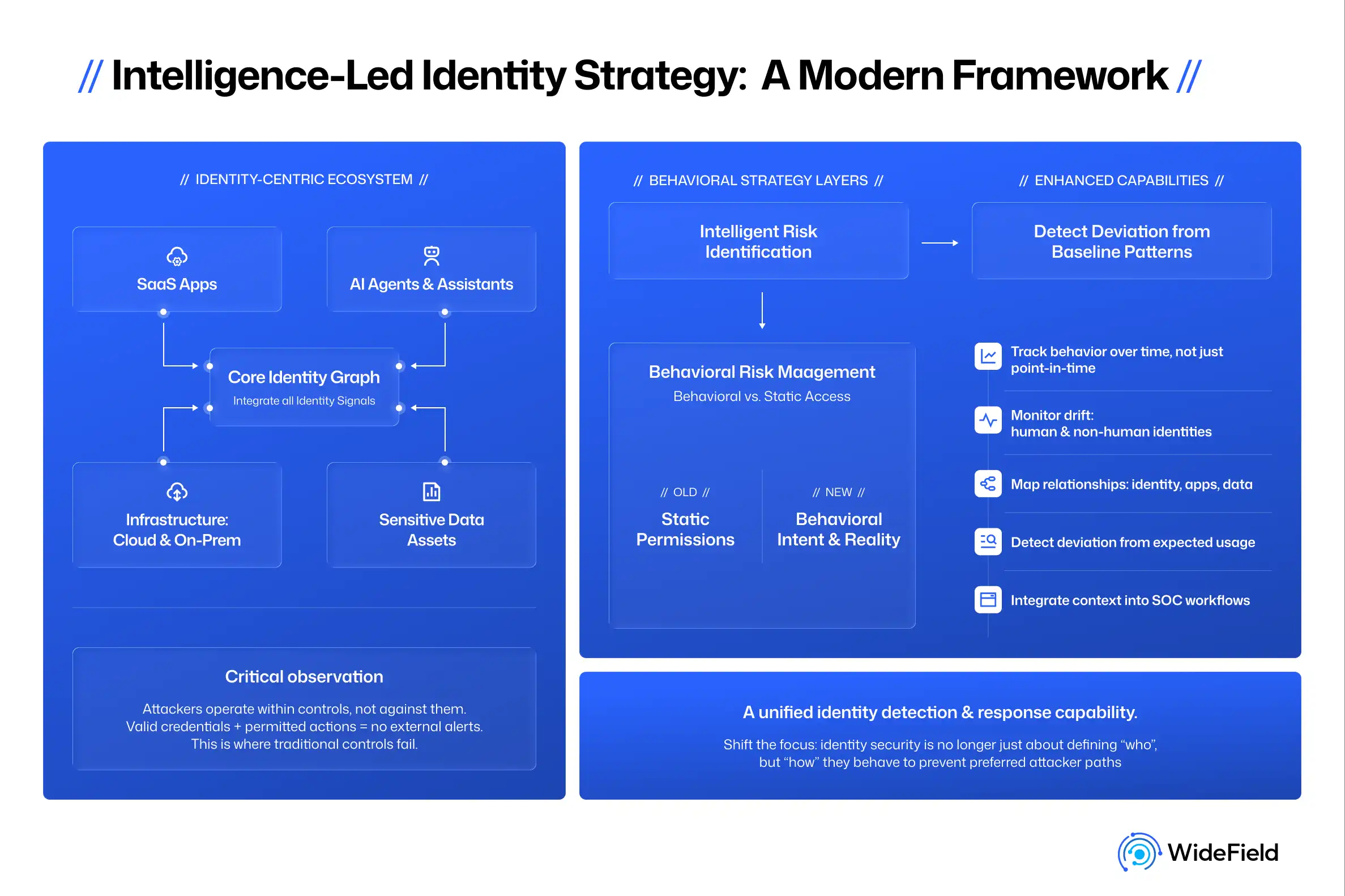
Identity supply chain security
The interconnected risk is high with identity supply chains such as federated trust or in this case of 3rd-party application vendors who by nature of the OAuth protocol have cached, virtually permanent access tokens due to the refresh token model. Similar risks unfolded with the Okta HAR file security incident where cached tokens were stored as part of HAR files within Okta support. We also saw this in the BeyondTrust-Treasury remote access breaches with API keys stored on the vendor side that gave access to Treasury desktops.
Better security logging by default
Better logging by default would help the detection and response for many cloud/SaaS breaches that abuse identities. Logging too often is designed by application developers, and useful only to the same developers. Security Ops needs better information geared around sessions and activities and compromise indicators. OAuth activity is notoriously lacking in logs. Workspace logs do not identify OAuth tokens which makes it difficult to trace specific session abuse. Salesforce activity logs are not available by default, but are an add-on as part of an expensive Salesforce Shield license. There are Salesforce customers who do not have adequate logging enabled due to the expense. The vendors need to focus on useful log telemetry, geared towards Security Operations, available by default.
Better sharing and coordination
Threat actors share much more than the organizations who are attacked or the vendors involved. The positives are that GTIG communication and coordination looks promising to share information to fully assess the incident. However, victim organizations and the vendors often have limited or no technical disclosures. The information such as the initial breach or access path to the data center would be extremely valuable for others to know in order to both address in their own data centers and also to fully assess the potential impact (how many apps and OAuth tokens were exposed and need to be contained).
The communications channels to reach appropriate SIRT teams at organizations can be a challenge in the best of times. In at least one case, a WideField customer’s marketing department received a security incident notice because the vendor had a marketing product and likely only had a marketing contact. The security team was not notified until weeks after the incident.