Agentic Identity Access Platforms: A CEO’s Field Notes
on the SACR AIAP Report
Software Analyst Cyber Research recently published a 92 page deep dive on what it calls Agentic Identity and Access Platforms. The premise is bold. As AI agents proliferate across the enterprise, we may need a new identity platform purpose built for them. A kind of new single sign on for agents.
It is an ambitious report. It is also one that deserves careful reading.
At WideField, we went through the analysis in detail. What follows is not a summary. It is a practitioner’s perspective shaped by real world deployments, customer conversations, and the uncomfortable edges where theory meets enterprise reality.
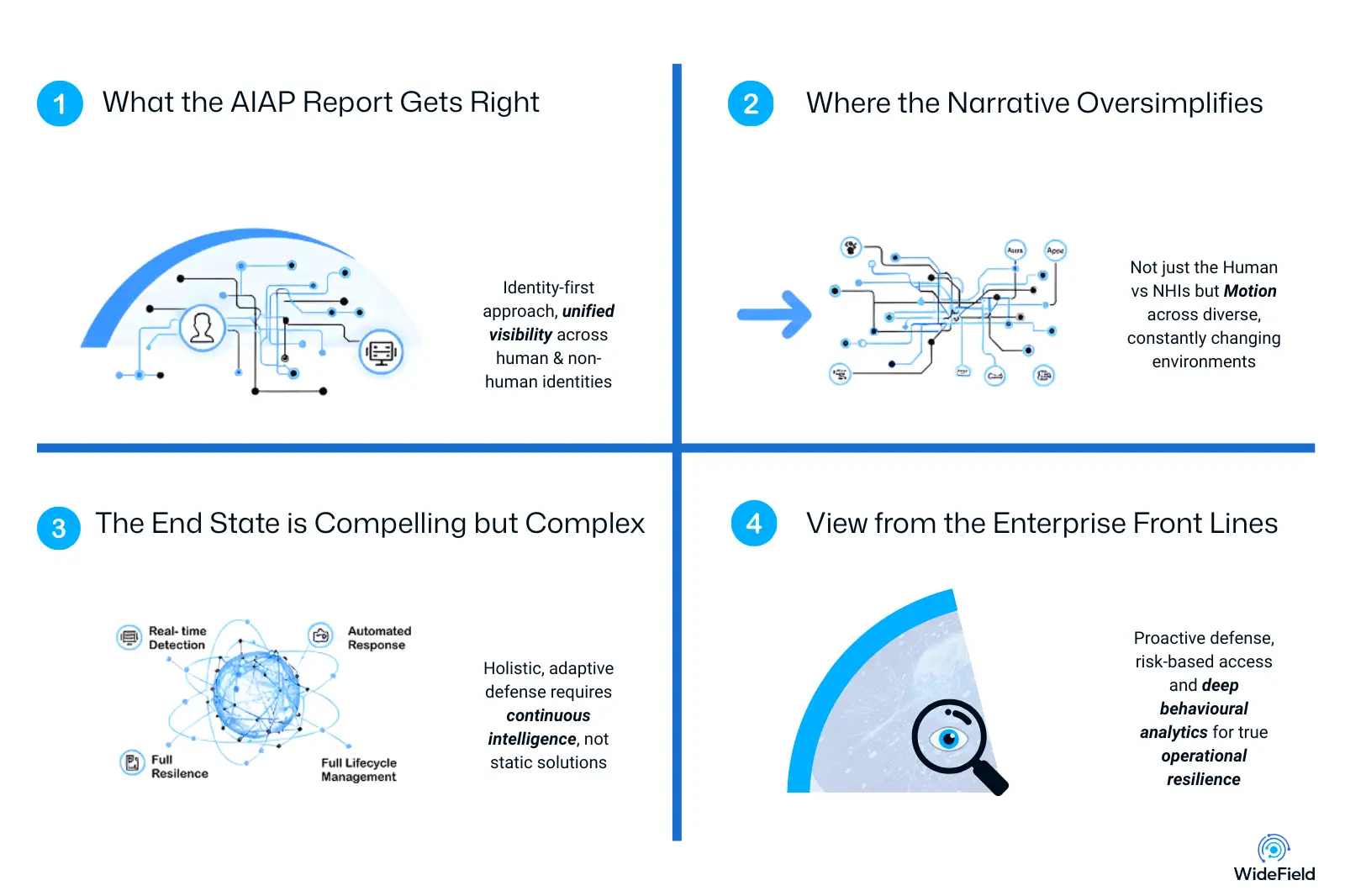

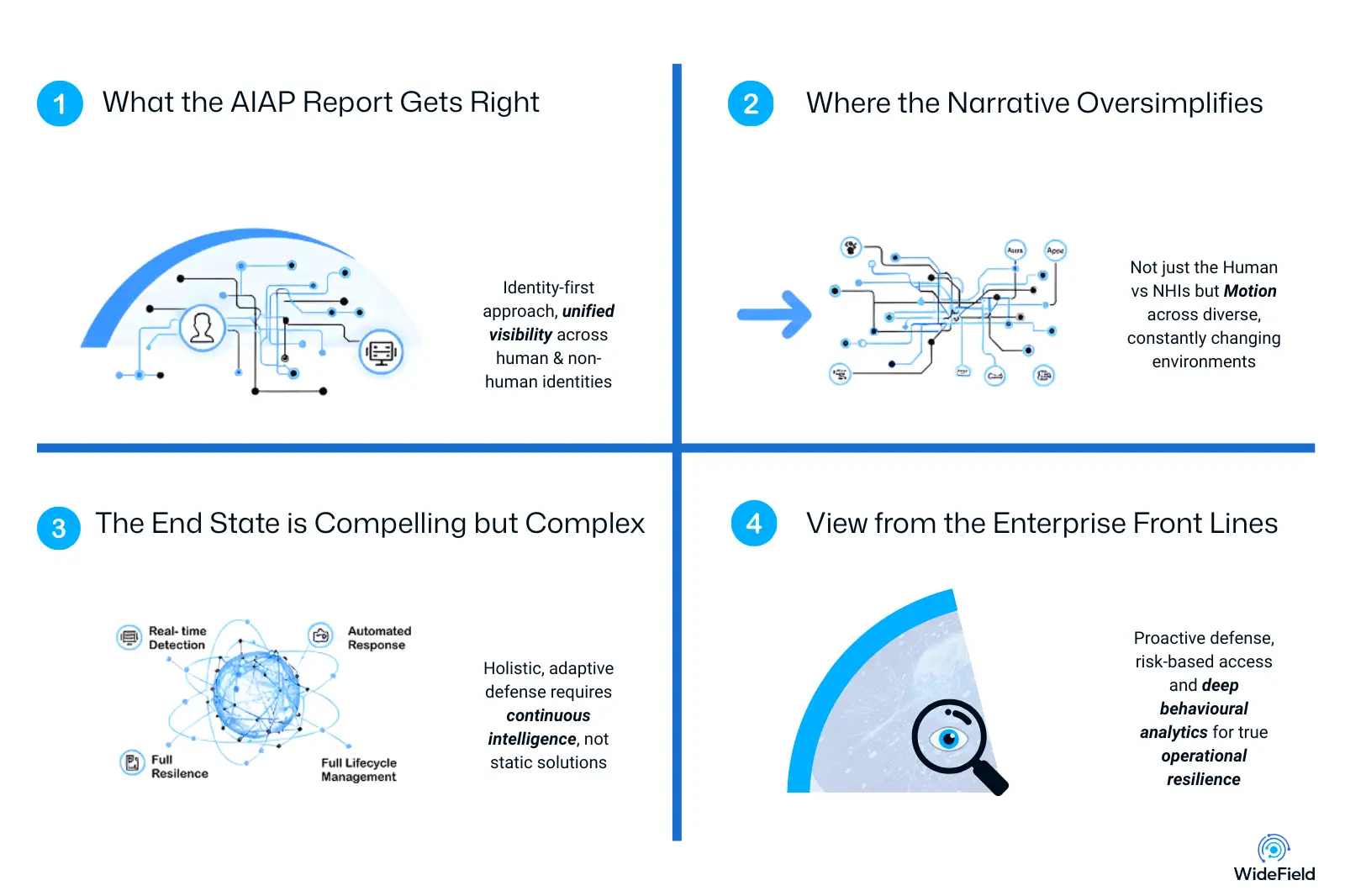
What the AIAP Report Gets Right
The report makes several observations that are fundamentally correct and important.
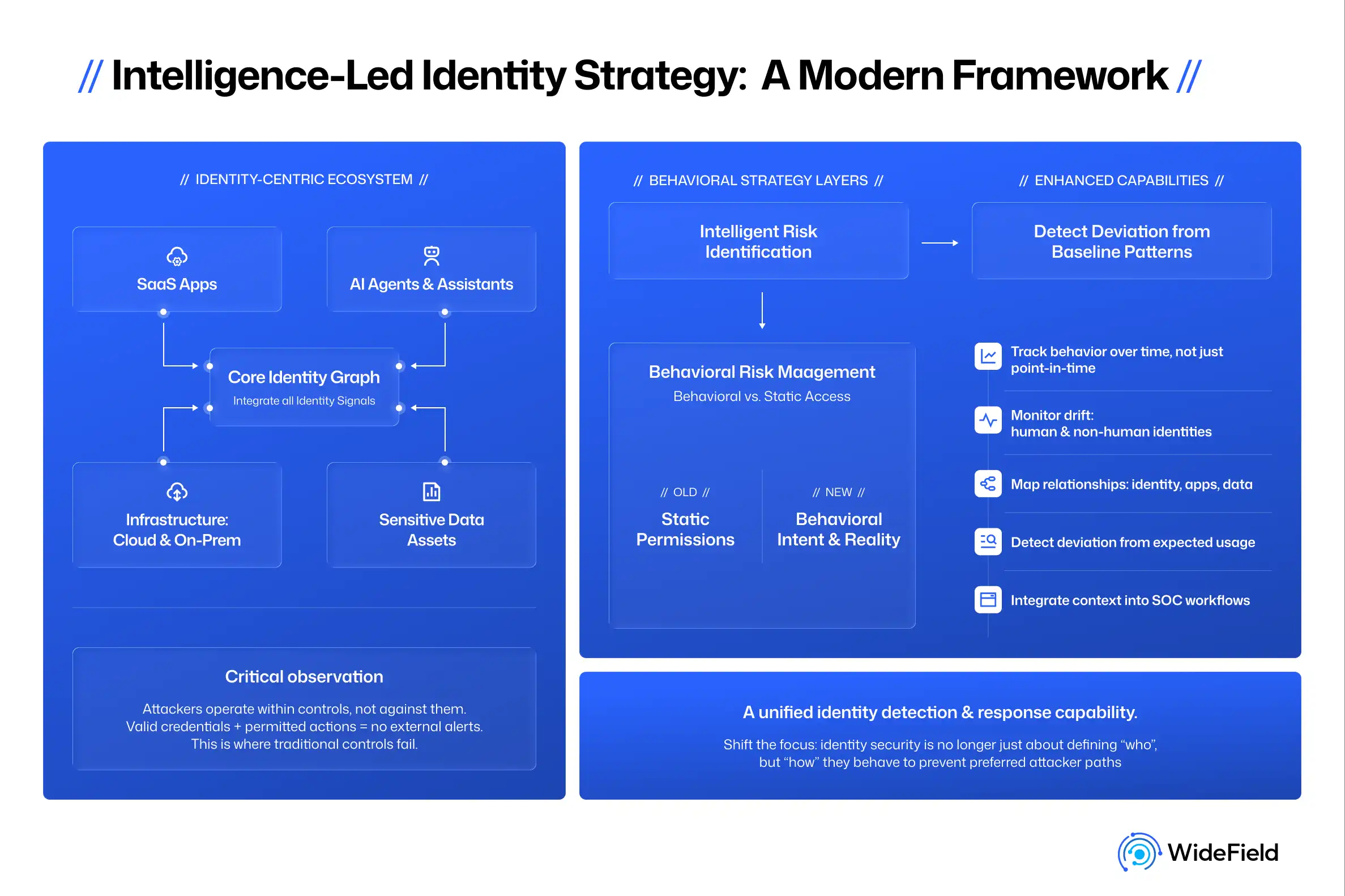
1. Agents Are Probabilistic and Non Deterministic
Unlike traditional automation scripts, AI agents do not behave the same way every time. They reason. They infer. They chain tools together. They may take different paths to achieve similar outcomes. That non determinism is not a bug. It is intrinsic to generative AI systems. It also makes identity and access control significantly more complex. Static models do not map well to probabilistic systems.
2. Agent Execution Is Multi Hop and Compositional
An agent does not simply execute a single function. It may call another agent. That agent may invoke a tool. That tool may call an API. Each hop introduces new identities, new tokens, new permissions. This chain of execution is precisely where traditional visibility models begin to break down. Identity is not a single event. It is a cascade.
3. We Need a New Model for Visibility, Orchestration, and Just in Time Privilege
The report correctly argues that agents cannot operate with standing privileges. If AI systems are to be trusted with enterprise data and workflows, permissions must be scoped, ephemeral, and context aware.
Visibility must go beyond authentication. Orchestration must account for task flow. Privilege must be granted dynamically and revoked decisively.
On these principles, there is strong alignment.
Where the Narrative Oversimplifies
The report positions legacy identity platforms such as Okta and Microsoft Entra as examples of an older architecture that solved password sprawl and SSO for humans.
That is true. But it is also incomplete.
Single sign on brokers authentication. It does not protect what happens after authentication. Once a human or non-human identity logs in using SAML or OIDC, the identity provider steps out of the picture. Consider a login into Slack or a similar collaboration platform. Sessions may last days or weeks. Post-authentication activity is largely invisible to the IDP. This is not a new problem exposed by agents. It is an identity problem we have lived with for years.
The same dynamic applies to agents. Authenticating an agent with an API key or token is the beginning. The real risk lies in what happens during long lived sessions and across chained tool calls. The report calls for a new SSO for agents. The deeper issue is post-authentication verification and continuous visibility. Without solving that, replacing the front door does little to secure the house.
Rethinking Agent Categories
The report classifies agents as user driven agents, delegated agents, and agentic apps. While directionally helpful, this framing risks flattening important distinctions.
There are at least two practical categories enterprises are grappling with today:
Off the Shelf Agents
These include commercially available systems such as Claude Code, Agentforce that connect to repositories, ticketing systems, and documentation platforms to assist with various tasks.
Organizations procure them. They configure them. But they rarely control how credentials are brokered internally or how permissions are scoped beyond what the vendor exposes.
Securing these agents is fundamentally about guard rails and oversight. How do you ensure they are not over privileged. How do you revoke sessions if behaviour becomes anomalous. How do you monitor data access across multiple SaaS systems.
Enterprise Built Agents
These are agents developed internally using platforms such as low code/no code frameworks like Microsoft Copilot Studio/ CrewAI or cloud AI frameworks like Bedrock or Azure AI foundry or Google Vertex AI.
Here, enterprises have far more control. They can register agents formally, assign identities, provision scoped access, implement just in time credentials, and apply lifecycle governance similar to non human identities.
This distinction matters. The control surface is different. The security model must reflect that.

The End State Is Compelling but Complex
The report envisions a central credential broker capable of discovery, inventory, ownership attestation, intent evaluation, scoped ephemeral credential issuance, and continuous policy enforcement.
That is a powerful north star.
Reaching it, however, will require deep ecosystem change.
Most cloud and SaaS providers still rely on OAuth based flows for non-human access. Fine grained scopes are inconsistent. In many cases, permissions remain coarse. If the only available scope is to read all mail, any agent connecting to an inbox inherits broad access.
To achieve true intent based and task scoped access, we will need:
- Richer, fine grained permission models from SaaS providers
- Standardised telemetry for agent actions
- Stronger integration between identity, EDR, and SASE systems
- Shared frameworks for marking sensitive operations
Without these building blocks, intent driven access remains aspirational.

WideField’s View from the Enterprise Front Lines
Enterprises are not asking for a theoretical new SSO. They are asking three practical questions.
1. How Do I Secure the AI I Already Deployed?
Development teams are experimenting with coding agents. Support teams are piloting AI assistants. Knowledge workers are connecting chatbots to internal repositories.
Leaders want guardrails. They want to know:
- What permissions does this agent have
- What data is it accessing
- Can I revoke access immediately if something goes wrong
At WideField, we focus on lifecycle visibility. From onboarding to session execution to revocation. Observability must span not only the first authentication event but every subsequent hop.
2. Do I Have Shadow AI Accessing My Data?
Shadow IT has evolved into Shadow AI. Agents and AI assistants may connect to corporate SaaS systems without central visibility into those connections.
Discovery and inventory are foundational. Before enterprises can enforce policy, they must understand which agents exist, which credentials they hold, and what systems they touch.
3. What Is My Risk Threshold for Autonomous Action?
Most organisations are not yet comfortable allowing AI to make production changes without oversight. Stories of AI deleting critical resources may be rare, but the fear is real.
A pragmatic approach is to mark sensitive operations and apply policy. For certain actions, require a human in the approval loopl. Over time, as confidence increases, policies can be relaxed.
Security maturity is iterative.
Why Auditing and Multi Hop Observability Matter Most
Agent security does not end at authentication. It does not end at token issuance.
It requires auditing every session. Tracking what data was read. What was written. How identities morphed as one agent invoked another. Where context shifted and permissions expanded.
If identity is the new perimeter, then agent observability is the new control plane.
The AIAP report has sparked an important conversation. It correctly identifies that agents represent a structural shift in how identity and access must function in the enterprise.
Where we differ is not in the destination, but in the path. Before we build a new SSO for agents, we must solve for post authentication governance, fine grained permissions, lifecycle control, and cross system observability.
The future of agentic identity will not be defined by a single platform. It will be shaped by how well we integrate identity, cloud, SaaS, and AI ecosystems into a coherent identity security fabric.
From a CEO perspective, the question is not whether agentic identity platforms will emerge. They will.
The question is whether we build them anchored in real enterprise constraints or in architectural abstraction.