ITDR is Dead. Long Live ITDR.
The threat landscape has evolved far beyond what a four-letter acronym was ever designed to handle.

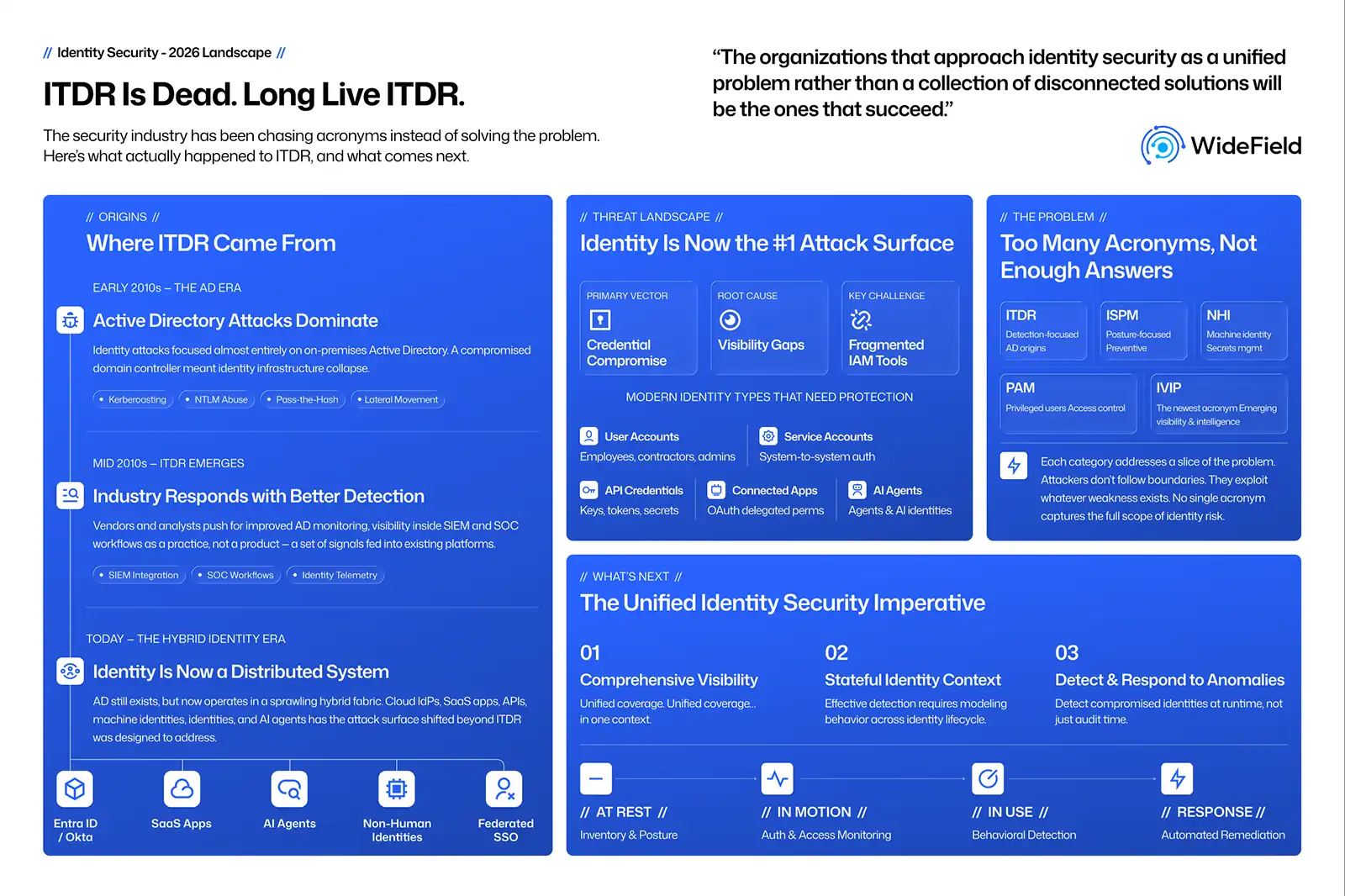
Every few years the security industry goes through the same cycle. A new acronym appears. Vendors rally around it. Analysts attempt to define it. Buyers try to understand whether they need it. And eventually, the industry realizes that the acronym was only pointing to a deeper problem that was never fully solved.
Identity Threat Detection and Response, or ITDR, is going through that moment right now. Many organizations asking "what is ITDR?" are finding that the answer is more complex than a ever.
So let’s start with a bold statement.
ITDR is dead.
But perhaps more specifically, ITDR was never supposed to be alive as a product category.
The Strange Life of a Category That Was Never a Category
Gartner has been very clear in its framing. Identity Threat Detection and Response was meant to be a practice, not a category. A set of tools, processes, and operational capabilities that use signals from existing systems such as SIEM, XDR, and other security telemetry platforms.
In other words, there was never supposed to be a standalone "ITDR tool" or a single set of ITDR solutions.
The thinking behind this definition was straightforward. If your organization is already collecting telemetry from endpoints, networks, and cloud systems into a central detection platform, then identity signals should simply be another stream of telemetry. Write the appropriate detections. Correlate the signals. Respond to the attack.
In theory, that sounds reasonable. In practice, it has proven to be far more complicated.
So now we find ourselves in an odd position. We're eulogizing something that technically was never supposed to be born. But we're also doing it at exactly the wrong time, because the identity threat problem has never been more dangerous, more complex, or more pressing.
The Orgins of ITDR
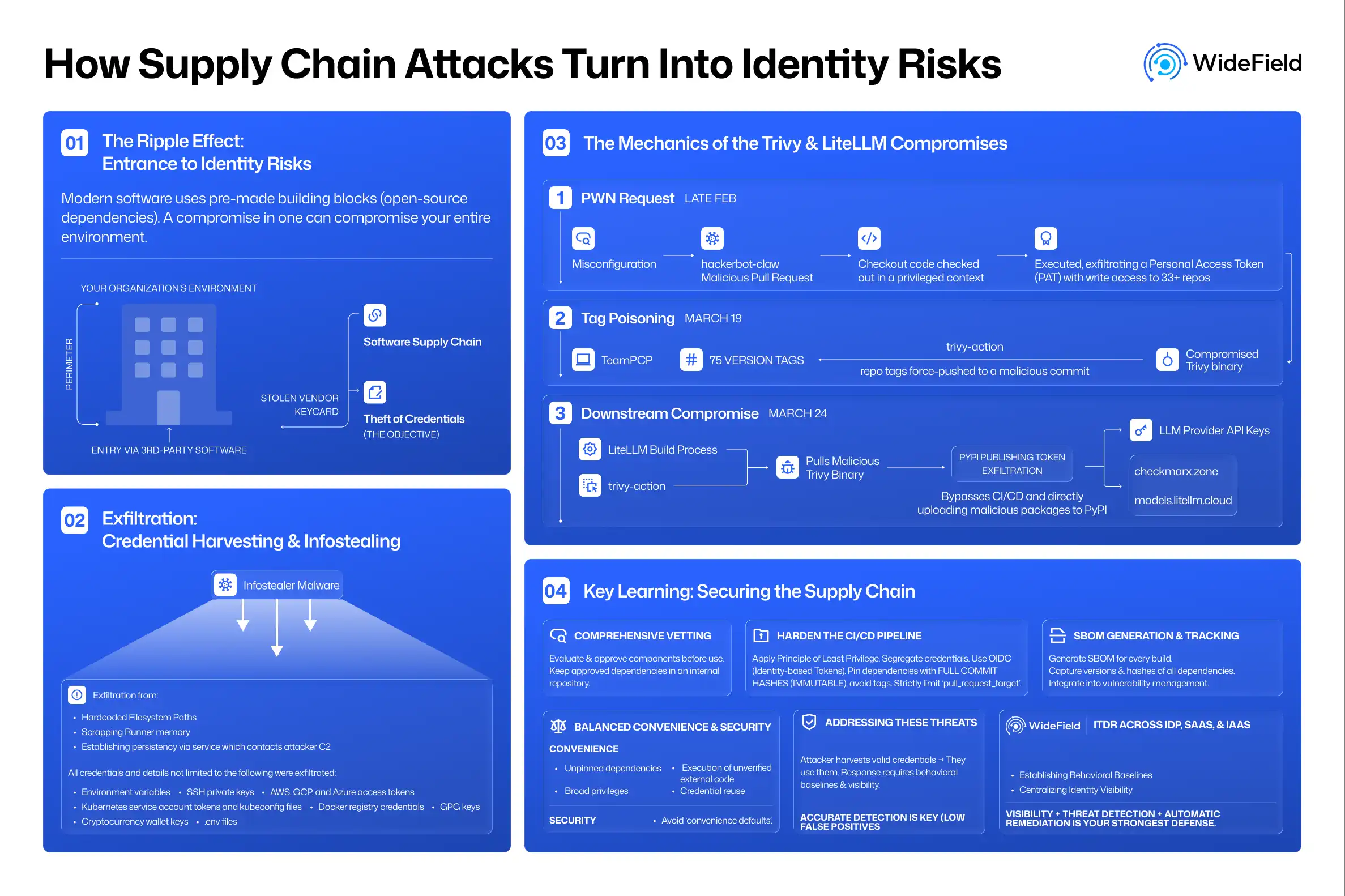
To understand what ITDR is and why it emerged in the first place, we have to go back a few years to when Active Directory attacks dominated the enterprise threat landscape. Techniques such as Kerberoasting and the abuse of NTLM were being used routinely by attackers to move laterally across environments. If an attacker successfully compromised a domain controller, the entire identity infrastructure could fall with it.
The industry responded by improving visibility around Active Directory abuse, strengthening monitoring of identity-related signals, and encouraging more robust detection logic inside SIEM and SOC workflows.
Since then, the architecture of identity has evolved. Active Directory still exists in most environments, but it now operates as part of a hybrid identity fabric. On-premises directories are synchronized with cloud identity providers such as Entra ID and often federated with additional SSO platforms. Identity is no longer a single directory; it is a distributed system spanning cloud platforms, SaaS applications, APIs, machine identities, and increasingly AI agents.
Identity Has Become the Primary Attack Surface
Recent research reinforces what many defenders already know from experience. Identity has emerged as the primary attack surface in modern enterprises driven by the explosive growth of human and non-human identities. Plus, how access is granted and managed has become more complex.
Here's what makes the identity security conversation so uncomfortable: the majority of high-profile breaches in recent years happened at companies that were well-resourced and had already deployed identity security technology. We're talking about organizations with SSO, MFA, and privileged access management. And attackers still got in. Worse, they went undetected for days, sometimes weeks. And in most cases, they didn't need sophisticated zero-day exploits to do it.
Credential compromise and account takeovers continue to occur with alarming frequency. Phishing campaigns, social engineering, and credential theft remain highly effective because identity systems sit at the center of almost every enterprise workflow.
Even as organizations adopt stronger user authentication methods, visibility gaps persist. Disconnected IAM tools, decentralized configuration decisions, and fragmented identity data create blind spots that attackers exploit. In other words, the problem ITDR was attempting to address did not disappear; it expanded.
Why the Practice Only Argument Breaks Down
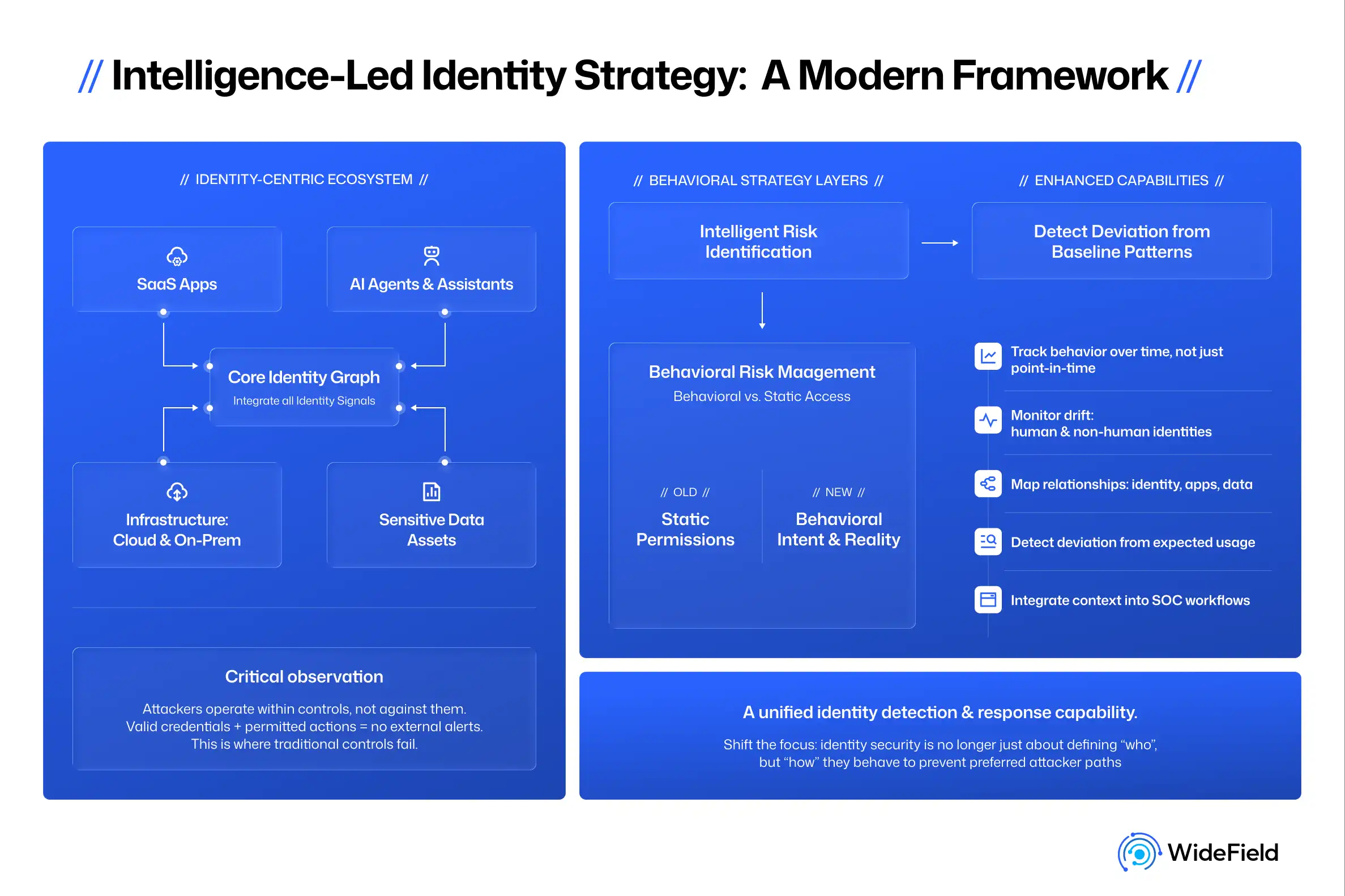
The idea that identity detection can simply live inside existing SOC tooling assumes that those platforms have the context needed to reason about identity behavior.
But identity is not just another telemetry stream.
Identity systems are deeply stateful. They carry context about who an entity is, what privileges it has, how those privileges were granted, and how access changes over time. A suspicious login event cannot be interpreted correctly without understanding the entitlements behind that identity, the relationships between identities and resources, and the policies governing access.
Expecting generic SIEM or XDR systems to fully model that context is similar to expecting endpoint detection platforms to secure cloud infrastructure without specialized visibility. The security industry recognized that limitation long ago, which is why categories such as EDR, NDR, and CDR emerged. Identity security presents a similar challenge.
The Real Problem With Identity Security Categories
Ironically, the answer is not simply to create another acronym. Over the past few years, the identity security platform market has become crowded with overlapping categories:
- Identity Threat Detection and Response (ITDR)
- Identity Security Posture Management (ISPM)
- Non-human identity (NHI) management
- Privileged Access Management (PAM)
- And, the newest one, Identity Visibility and Intelligence Platform (IVIP)
Each of these attempts to address a portion of the problem. None of them captures the full scope of identity risk.
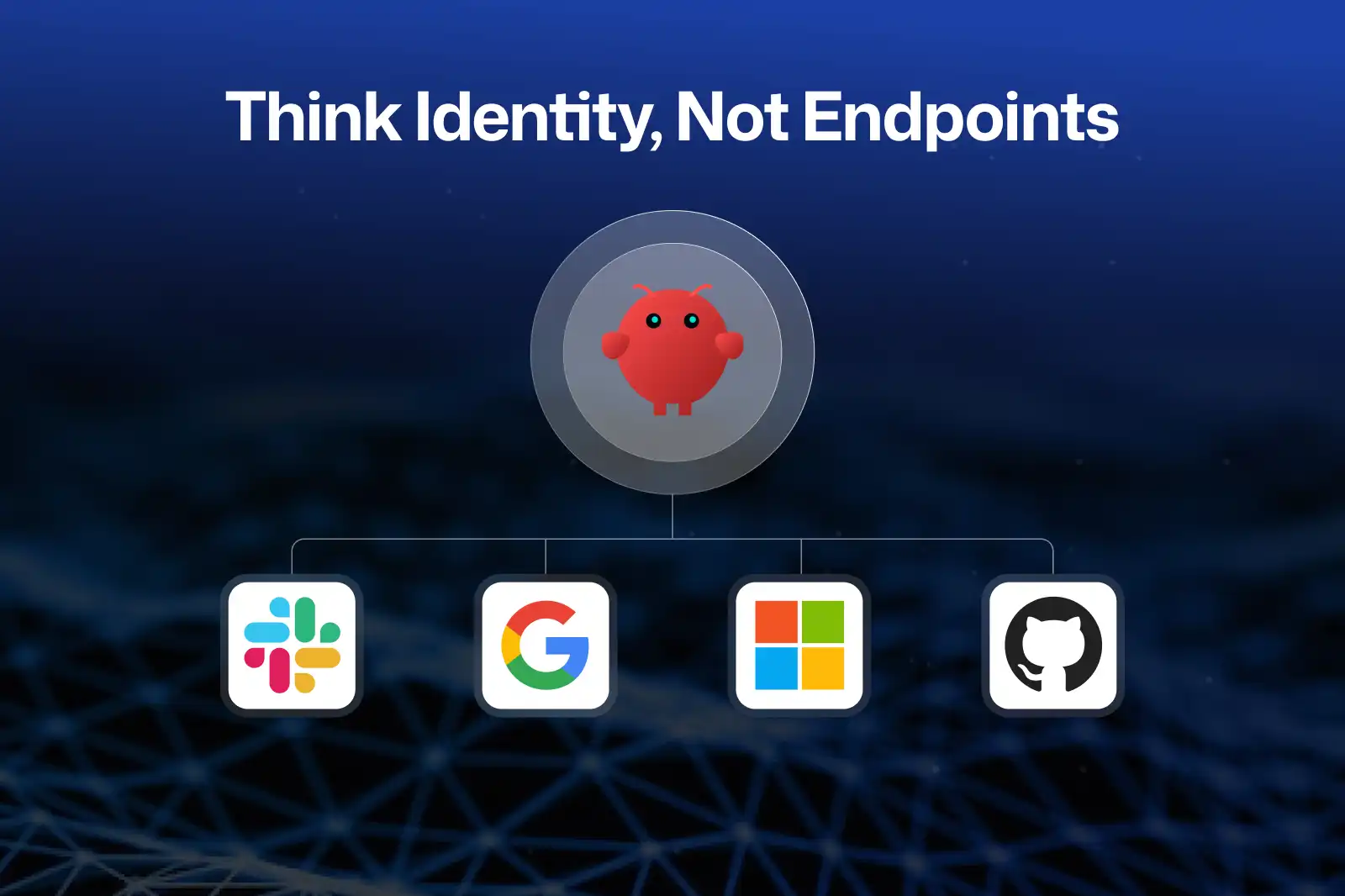
Attackers certainly do not think in categories. They exploit whatever weakness exists. Sometimes it is a posture issue, such as a misconfigured policy. Sometimes it is a compromised credential. Sometimes it is a malicious application that receives delegated permissions. Increasingly, it may be an automated workload or an AI agent operating with excessive privileges.
From an attacker’s perspective, all of these are simply ways to compromise identity.
The Next Phase of Identity Security
If we step back from the acronym debate, the question becomes much simpler: How do defenders know when any identity has been compromised?
An identity could be a user account, a service account, an API credential, a connected application, or an AI agent. Solving identity security requires visibility into all of them across their entire identity lifecycle—at rest, in motion, and in use.
Moving Beyond the Acronym Game
Security leaders do not need another four-letter acronym. They need a modern approach to identity security that reflects how environments operate today. That approach must provide comprehensive visibility across human identities, agentic AI, and all other non-human identities. It must detect identity-based attacks and anomalous behavior as identities interact with systems.
Instead of arguing about categories, the industry should focus on solving the underlying challenge. Identity security is the next major frontier in cybersecurity defense. The organizations that approach it as a unified problem rather than a collection of disconnected authentication solutions will be the ones that succeed.