// Blogs//
Wide Views on Security
Threat Intelligence
//
April 21, 2026
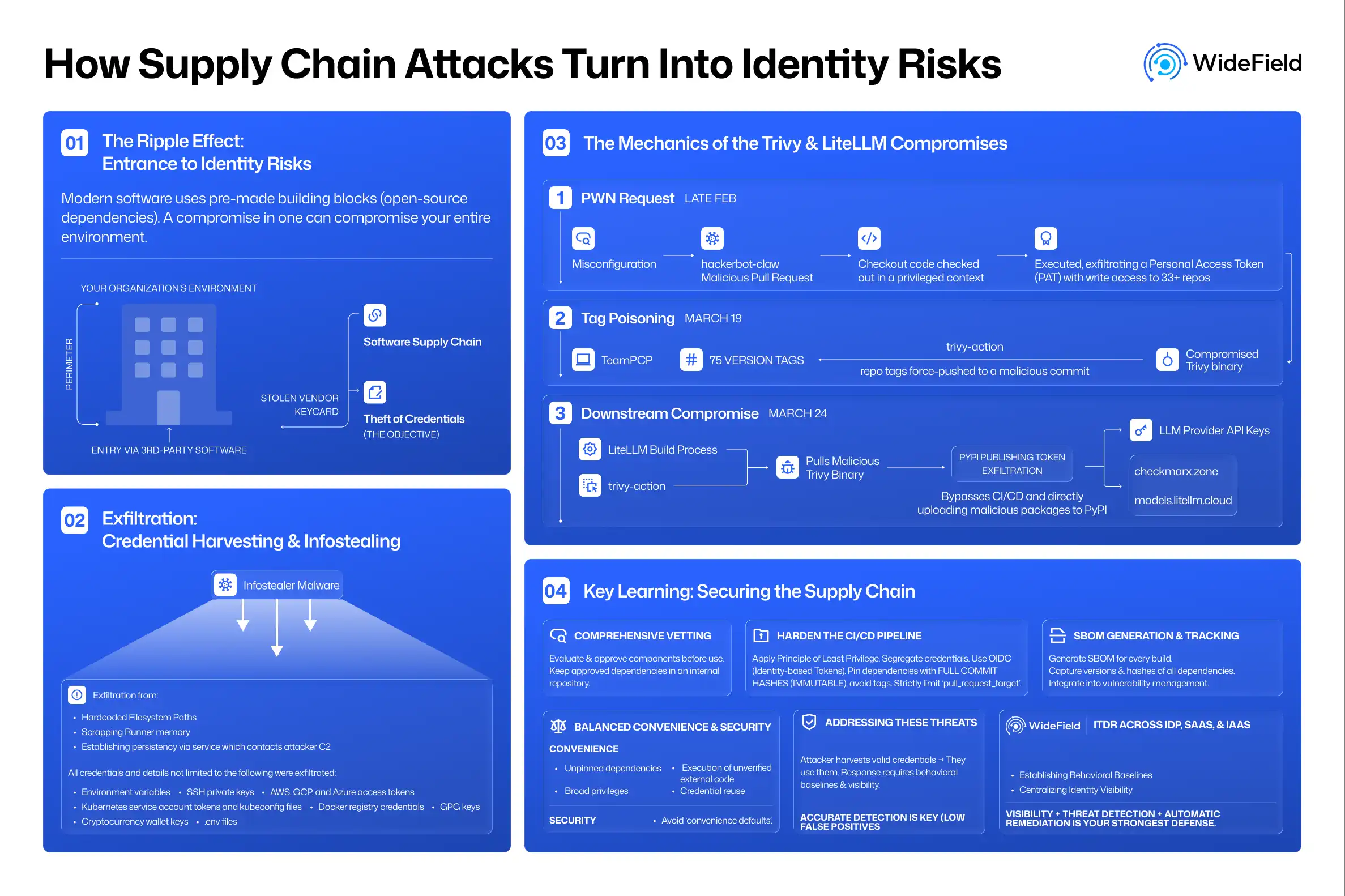
How Supply Chain Attacks Turn Into Identity Risks
In a supply chain attack, the developer of the tool is rarely the final target.
Read Article
Latest articles
// Get in touch //
Get started in minutes. Address identity risk in hours.
Deploy WideField in minutes and get a complete identity risk assessment in a single day. Connect your stack, analyse threats, and start reducing risk—fast.
Request a Demo